Table of Contents
Memory mapping is a technique to bind user-generated addresses to physical addresses in the memory. This requires static binding or dynamic binding.
CPU gets instruction from memory, and then decode the instruction during the instruction-execution cycle. The instruction also contains the memory address of operands that need to be fetched. The CPU finished the instruction and saves the results back to memory. The memory unit only sees streams of addresses and does not know how they are generated.
Memory Hardware
A CPU can only access registers and memory directly. The processes that are on disk must be brought to memory before CPU operates on them.
There is two concern for the CPU:
- The speed of access to memory.
- The memory protection.
The CPU is fast compared to memory, if the data is not available to CPU, it tries to access the memory or it will remain idle or stop working. To increase the speed of access a fast memory called cache is included in the system which stores frequently used data.
The memory protection is implemented by CPU using two registers – base and limit. The base contains the lowest physical address and limit contains the range of address.
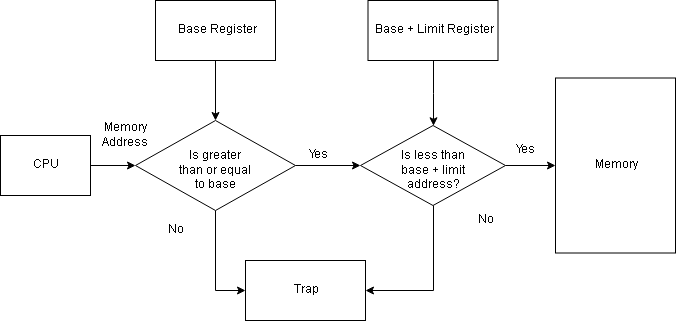
Each user-generated address is compared with the base and limit to determine the legitimacy of the address. A trap is generated if the user process tries to access OS memory. The OS runs in privileged mode or kernel mode and has full access to all the memory.
Memory Mapping Techniques
A program is bought to memory as process and keeps moving between disk and memory, depending on the memory management. All processes waiting to be loaded into memory form an input queue.
Normally, one process is selected from the queue and it is executed in memory. When the process terminates, its memory is free.
The system allows the user process to reside in any part of the physical memory. The memory starts at 00000, but the user process starting address need not be 00000.
The user process goes through several mapping steps before it gets executed:
- The address at source code is symbolic addresses. E.g total = 23;.
- The compiler binds the symbolic address to relocatable addresses ( e.g 10 bytes from the beginning of this module).
- The linkage editor or loader will in turn bind the relocatable address to absolute address such as 43267.
The binding is a mapping of one address to another which can be done in many ways;
Compile time mapping
If you already know that a process will start at memory location M, then compiler code will start at that location and generate absolute code directly. The code and data references are mapped to physical addresses when program is compiled. If the location changes then, recompile the code.
E.g MS-DOS.COM-format programs are bound at compile time.
Load time mapping
If the memory location of the process is not known, the compiler must generate relocatable code. This binding process adds a starting address of the process to each reference in the program. The process will not move to another memory location during execution because starting address must remain the same. If starting address changes, reload the user code to incorporate the change. The final binding is delayed until load time.
Execution time mapping
In this method, a virtual address is mapped to a physical address. If the process can be moved from one memory location to another, then binding is delayed until runtime. It requires special hardware and most OS use this method.
References
- Linda Null, Julia Lobur (December 17, 2010) The Essentials of Computer Organization and Architecture, 3rd edn., Jones & Bartlett Learning.
- Abraham Silberschatz, Peter B. Galvin, Greg Gagne (July 29, 2008) Operating System Concepts, 8 edition edn., Wiley.