OS provides the computing environment. They are organized in many ways in different systems, but a few things are common for all OS.
In a single user system, the CPU sits idle when I/O is working or vice-versa. The CPU utilization increase with multi programming systems. A subset of jobs from a pool of jobs on the disk is loaded into the memory. The CPU executes one of them if the job has to wait for CPU switch to another job and later come back to the first job when the wait is over.
Different Systems
The multiprogramming system does not allow user interaction with the system. A time-sharing system allows multiple users to interact with the system directly. The time-shared computer switches between programs from different users so frequently that it gives an impression to the user that the entire system of dedicated to him.
The multiprogramming and time-sharing system must make decisions about two things:
1. several jobs ready to be brought to memory from the pool. (job scheduling)
2. several processes ready to run at the same time. (CPU scheduling).
The time-sharing system gives good response time by swapping process in or out of disk. Another method is a virtual memory scheme which abstracts physical memory into much larger logical memory. thus allowing programs larger than physical memory to run without problem.
Time-sharing system must provide a file system on the disk. It must also ensure that operations are synchronized and processes are cooperating. The system must prevent a deadlock situation.
Operating System Operations
Modern OS is interrupt driven. OS waits for events that are created by an interrupt or a trap. A trap or an exception (divide by 0) is a software interrupt caused by an error or user program request for specific OS services. An interrupt service routine from OS handles the interrupt.
OS and user programs share common resources, any erroneous program can change other programs, or data of other programs, or even OS itself. Therefore, some kind of protection is necessary to protect OS codes.
Dual-Mode Approach
To protect OS codes, we must be able to distinguish the OS-specific codes and user-defined codes. The computer hardware can differentiate the codes. It is divided into two modes of execution – user mode and kernel mode. The kernel mode is also known as supervisor mode, system mode, or privilege mode. A mode bit is added to computer hardware to indicate the current mode – kernel(0) and user(1).
When the user is executing an application, it is in the user mode and when the application requests an OS service (system call) it is in kernel mode.
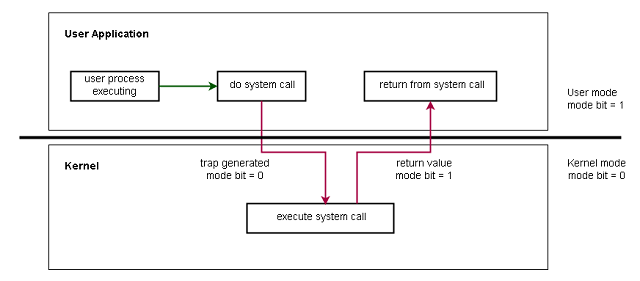
The system boots in kernel mode and runs an application in user mode. When a trap or an interrupt happens the mode bit is set to 0 before transferring the control to OS for system calls. The mode bit is set to 1 when OS returns to the user program. The hardware ensures that faulty program does not run instructions in privileged mode, and only privileged instructions must run in kernel mode, otherwise, consider that illegal and generates a trap.
Except for MS-DOS, all modern operating systems such as Windows XP, Windows Vista, Windows 7,8,10, Unix, Linux supports dual-mode of protection.
Operating-System Services
An operating system manages the computer system resources for smooth and efficient execution of user applications. An OS provides services such as
- Process management
- Memory management
- Storage management
- Caching
- I/O system
Process Management
A process is a program in execution that needs CPU time, memory, and i/o systems. The user process is different from the system process because the system process belongs to OS. The process management activities of OS are:
- Process and thread scheduling for CPU.
- Creating and deleting processes.
- Changing process states – Suspending and resuming.
- Process synchronization for concurrency.
- Process communication – interprocess communication.
Memory Management
The memory management task deals with managing the main memory which is a large array of words with each word having its own address. During the instruction-fetch cycle, the CPU read instructions from the main memory, and during the data-fetch cycle, it read data from the memory. If the data is on the disk then it must be brought to the main memory because CPU has direct access to main memory.
A program is also loaded from disk to main memory so that the CPU can read the instructions and data as mentioned earlier. Once the program terminates, the memory is free and available to other programs. Since several programs run in memory, there is a need for memory management scheme which many factors such as system design, hardware support, etc.
The memory management activities are:
- Track which memory location is used and by whom.
- Decide which process and data to move in or out of memory.
- Allocate or Free (deallocate) memory as required.
Storage Management
The storage management is about preserving information that is not in main memory. The storage device keeps information in the form of bits or bytes. However, the OS gives a logical view of this information in the form of files. There are many types of files depending on what information gets stored there – text, image, or video. So the main task of OS is file management.
The file management activities are :
- Create or Delete files
- Create or Delete directories for file organization.
- Support all primitives storage technologies for file or directory manipulation.
- Mapping files onto secondary storage(disk).
- Backing files on a stable storage device.
- Free-space mangement
- Storage allocation.
- Disk scheduling.
Caching
The caching is faster memory and the first place where CPU looks for information. It is because the main memory is slower most of the time, so if need any information quickly it is kept in cache for quick access. This avoids the need to access the main memory again for the same information.
Cache management is a design problem, we must select the right cache system – software cache or a hardware-based cache and replacement policy that decides which information to be stored in the cache. The size and replacement policy of the cache can also increase the performance of a system.
I/O Systems
The role of OS is to hide details of hardware devices from the user. In Unix, the details of devices are hidden from OS itself by the I/O subsystem. The I/O subsystem consists of :
- A memory management component that does spool, buffering and caching.
- A device driver interface.
- Drivers for specific devices.
All device-related tasks are controlled by device drivers, and only it knows the peculiarities of the device.
Protection and Security
Access to data must be regulated due to multiple users and concurrent execution of processes.
For example,
- Memory addressing hardware ensures the process runs in its own address space.
- The timer ensures that the process must relinquish its control after some time.
- Device control registers are inaccessible to users thus protecting the peripheral devices.
Protection is controlling access to resources by processes and users. OS must specify the controls and give means to implement these controls. Protection-oriented systems can distinguish between authorized and unauthorized users but still fails due to inappropriate access.
Security incidents are common in computing environments. In such cases, the OS must defend the system with proper security. The modern OS maintain a list of UID (user identification) numbers or user IDs with a password to secure the system. Sometimes, the user identification is made of SID (security ID).
The modern file system allows users to set access rights for the files they create or own. They can give read, write, and modify or any combination of these three.
References
- Abraham Silberschatz, Peter B. Galvin, Greg Gagne (July 29, 2008) Operating SystemConcepts, 8 edition edn., Wiley.
- Tanenbaum, Andrew S. (March 3, 2001) Modern Operating Systems, 2nd edn., Prentice Hall.
